Blackouts all over the USA. Every time we have a Thunder Storm... Hmmm I wonder???
Don
Posted by THN Reporter On 3/22/2012 11:55:00 AM Face to Face with Duqu malware
Once again we discuss about Stuxnet, cyber weapons and of the malware that appears derivate from the dangerous virus. The international scientific community has defined a Stuxnet deadly weapon because been designed with a detailed analysis of final target environment supported by a meticulous intelligence work that for the first time in history has embraced the world of information technology.
The agent was designed with the intent to strike the Iranian nuclear program and even more clear is who has always opposed such a program, U.S. and Israel first, and consider also the technology skill necessary to develope a weapon with the observed architecture is really high.
Extremely important two factors af the event:
1. the choose of control systems as target of the malware.
2. the conception of the virus as an open project, a modular system for which it was designed a development platform used to assemble the deadly cyber weapons in relation to the final targets.
Regarding the second point, it has been discovered a platform behind Stuxnet called “Tilded Platform“, used also for the development of Duqu malware, and that make possible the development of a set of reusable tools, a true innovation that make possible the composition of ever new and enhanced agents with modules developed to fulfill specific functions against clearly defined targets.
As previously stated Duqu has some interesting features such as:
- Modularity of its structure.
- In isolated instances of the malware, unlike Stuxnet, it would not seem to be equipped with modules for SCADA systems attack. It is only able to steal information from the host system.
- The malware, such as Stuxnet has characteristics that demonstrate innovative techniques behind its development. We suppose that a team of specialists with high technical skills has been engaged to project the most innovative cyber weapon.
According the ENISA Duqu Analysis there are important differences between Duqu and Stuxnet. The 2010 Kaspersky analysis [Gostev 2011] concluded that Stuxnet consists of the two parts:
1. A component responsible for the propagation of the malware (a carrier platform).
2. A separate module targeting Programmable Logic Controllers (an attack module).
According to Kaspersky, the carrier platform of Stuxnet could be reused, for example with a different attack module. But, unlike Stuxnet, DuQu can also be reconfigured remotely to install new malware payloads and to direct attacks at new targets.
The attack module of DuQu, found together with the detected samples was a general purpose keylogger (enriched with some additional spying capabilities) able to perform a reconnaissance in any organization. However, according to Symantec, the aim of DuQu is to infiltrate organizations operating in industrial environments. This conclusion is based on the fact that the majority of the detected threats were found in industrial infrastructures, and because of the connection to Stuxnet code. Unlike Stuxnet, DuQu is an intelligence gathering tool, apparently aiming to prepare the ground for attacks such as Stuxnet. It should be emphasised, however that there is no direct evidence for the intentions behind DuQu
But if Duqu has no components to attack SCADA systems or similar, why create in us so much worry? Remember that we defined modular Duqu? Well this is the feature I think that should cause us to jump from the chair. To date we have isolated versions of malware orphan of those components to attack specific critical systems, but it is reasonable to assume that the same Duqu is a work in progress project. The ability to compose its structure at different times using modules designed specifically for precise goals, makes this unique and formidable.
What occurred in the Stuxnet case has raised media attention demonstrating the total inadequacy of the defense systems of critical infrastructures across the world. Many, too many, the SCADA systems around the world, achievable in an easy manner and easily attacked by evil-minded because they are un protected, exposed on the web for maintenance purpose, and configured with the factory settings easily available even with simple searches on the web. Also for that SCADA systems deployed without security and isolated from the Internet there is a concrete risk to be infected using USB memory sticks.
While in recent weeks, the Iranian government declared definitively defeat the threat Stuxnet in the last month there are many news published on the web related to malware Duqu.
The mistery of Duqu sorce code
The first one was related the identification of the mysterious language used in the DuQu virus. Researchers at Kaspersky Lab requested the help of international experts after failing to figure out the language on their own.
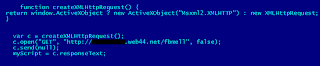
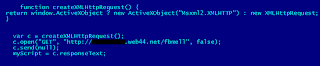
Thanks to help from programmers has been discovered that the language, which DuQu used to communicate with C&C (command & control) servers, is a special type of C code compiled with the Microsoft Visual Studio Compiler 2008.
Despite the long period of study conducted on the agent the component of the source written in C remained a mystery. It's a vital part for Duqu used to communicate with C&C servers, download additional payload modules and execute them on infected machines.
The code was C code compiled with Microsoft Visual Studio Compiler 2008 using options 01 and Ob1 in the compiler to keep the code small optimizing execution time and size of the source code.
The use of object-oriented C dialect, generally called “OO C, to write the event-driven code in the malware reveals that authors who coded this part of DuQu were probably old-school programmers, their style is uncommon for malware and is more commonly found in professionally-produced commercial software created ten years ago, according Costin Raiu, director of Kaspersky Lab's global research and analysis team.
Another important factor in choose of C language instead other more powerful like C++ it the necessity to grant portability of the agent that maybe must be compiled with several standard compiler in different environments. This requirement indicate us that the agent could be used to attack other platforms, not necessary Widows based.
“Obviously when you create such a complex espionage tool, you take into account that maybe some day you will run it on servers, maybe you will want to run it on mobile phones or God knows what other devices, so you just want to make sure your code will work everywhere,” Raiu says.
The Duqu evolution
News of these days is that a new variant of Duqu has been isolated, the event confirm the hypothesis made on the evolution of the malware, a work still in progress that will propose in the next year several instances customized to attacks specific targets. The variant found was designed to evade detection mechanism of antivirus products and other security systems. Vikram Thakur, principal security response manager at Symantec, announced that the new Duqu Driver has been identified, let's remind that the module is used for loading the malware's encrypted body stored on the systems. The driver is called mcd9x86.sys and it was compiled on Feb. 23.
What is changed in the new driver?
The source code appears to be reshuffled and compiled with a different set of options and it also contains a different subroutine for decrypting the configuration block and loading the malware's body. A similar operation has been already observed in October 2011. Of course also the references to C&C server are changed because all old structures were shut down on Oct. 20, 2011.
Unfortunately the addresses of this server are not known because principal security firm don't have the full Duqu body but only the loader in the form of the driver, the loader does not contact the C&C directly, it only loads the main body which is stored in encrypted form.
What we expect from the future?
Surely we will confront with new and dangerous cyber threats that can offend the military and also private sector. Agents such as Stuxnet and Duqu are children of an ambitious and complex project that wants to be able to provide an "evolutionary" threat. Prepare to have to deal with new modules and new features designed to attack specific targets.
Let me raise serious doubts on the immediate effectiveness of preventive measures against this new generation of cyber weapons because the industry in general is still too vulnerable. Possible evolutions of malware could cause serious damage to infrastructures that use the systems in question.
The only way to emerge unscathed from this awkward situation is a close collaboration between industry, leading manufacturers of control systems and governments, hoping that security will become a requirement in the design phase.
Submitted By : Pierluigi Paganini
About the Author : Pierluigi Paganini, Security Specialist
CEH - Certified Ethical Hacker, EC Council
Go there...
http://thehackernews.com/2012/03/face-to-face-with-duqu-malware.html
-

Microsoft censors The Pirate Bay links on Windows Live Messenger
-

A Russian Zeus attacker Sentenced from Million Dollar Fraud
-

Chinese hacker arrested for leaking 6 million logins from CSDN
-
Facebook profiles can be hijacked by Chrome extensions malware
-

Return of Lulzsec, Dump 170937 accounts from Military Dating Site